Listening to music can have a positive impact on our brain. A study published in the journal of Neuroscience of Behavior and Physiology found that a person’s ability to recognise images, letters, and numbers was faster when rock or classical music was playing in the background compared to when there was no music. And of course, music improves our mood because it triggers the release of the “pleasure chemical” Dopamine.
But what most organisations don’t realise is that, while music can have a positive impact on its employees, the media players employees use to listen to their music of choice, or watch videos, can expose them, their machines, and the organisation to risk of exploits and advanced malware infections.
Killer Music: Hackers Exploit Vulnerabilities in Media Players to Infect User Machines with Advanced Malware
Trusteer’s research has shown that vulnerable media players are constantly targeted by malicious actors. Since in most environments media players exist on users’ desktops for their own personal use, IT and security administrators ignore these applications and the content files they use. After all, you want to keep your employees productive and happy, and allow them to listen to their harmless music while they work. However, because these applications are not controlled, and users are not in a rush to patch these applications, most installations are vulnerable to exploits.
A Media Player is a software program designed to play multimedia content as it streams in from a website, or from local storage or other resources. Some employees use the media players that arrives with the operating system – like Windows Media Player, while others prefer to download a different media player and install it on their workstation. But both the OS provided players and the downloaded players contain vulnerabilities that can be exploited to deliver malware and infect the user machine.
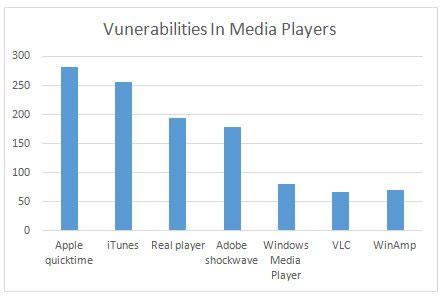
According to the National Vulnerabilities Database (NVD), over 1,200 vulnerabilities were discovered in media players since 2000. Most of these vulnerabilities were
engineering schemes. Typical examples include “promotional videos”, links to “free” song downloads and more.
Exploits Targeting Media Players Exist In the Wild
This is not a theoretical threat. Over the past few years we have seen exploits targeting both known and unknown zero-day vulnerabilities in media players. It is important to note that many exploits target known vulnerabilities for which a patch exists. As long as the patch is not deployed to mitigate the vulnerability, or some other controls are implemented to prevent the exploit, the media player is vulnerable to exploits and drive-by download attacks.
For example, here is a story about Drive-by-download attack exploits a known critical vulnerability in Windows Media Player:
On January 10th, 2012, Microsoft released a security fix for to address the MIDI Remote Code Execution Vulnerability (CVE-2012-0003) in Windows Media Player as part of its monthly patch cycle. Microsoft explained at the time that "An attacker who successfully exploited this vulnerability could take complete control of an affected system."
A couple of weeks later, security researchers found an active drive-by download attack that exploited the known vulnerability. The attack used a malicious HTML page to load the malformed MIDI file as an embedded object for the Windows Media Player browser plug-in. If successful, the exploit silently downloaded a Remote Access Trojan (RAT) on the user’s machine, without the user’s knowledge.
Protecting Media Players against Weaponized Content and Exploits
The general best practice is to always apply security patches to vulnerable applications as soon as they become available. But this is not applicable when the vulnerabilities is a zero-day vulnerability – a vulnerability that is not publicly known and therefor an appropriate patch doesn’t exist.
For effectively protecting employee endpoints and enterprise network against exploits and advanced malware, organizations should consider implementing a solution like Trusteer Apex. By disrupting the exploit chain of events, Trusteer Apex prevents the delivery of malware via exploitation of both known and unknown vulnerabilities in popular media players. Because it is not dependent on patch availability, or advanced threat information about its source, the vulnerability it exploits, or the malware that it tries to deliver in order to compromise the machine, Trusteer Apex effectively blocks attacks that attempt to exploit vulnerable media players and prevents the malware infection.






