Imperva have found that hackers are now using Remote and local file inclusion (RFI/LFI), as their favourite hacking method. With RFI/LFI attacks making 21 percent of all observed application attacks, which allows an attacker to target the computer servers that run Web sites and their applications, what can we do to stop this kind of attack?
Why is RFI/LFI attractive to hackers? A successful attack allows the execution of arbitrary code on the attacked platform’s web application. With RFI/LFI, a hacker can take over a web server.
Surprisingly, however, RFI/ LFI has not been taken seriously by the security community. In real-world hacking attacks, RFI/LFI attacks made up 21 percent of all observed application attacks.[1]
For hackers RFI/ LFI attacks are very attractive since they target are PHP applications. With more than 77% of today’s websites running PHP, RFI should be on every security practitioner’s radar—but isn’t. Some notorious RFI/ LFI examples include:
- Lulzsec using RFI bots to attack their targets.[2]
- Timthumb, a WordPress add-on, which was vulnerable to LFI and paved the way to 1.2 million infected websites. [3]
In one hacker forum, several discussion shed light on the value of RFI/LFI:
Why isn’t LFI/RFI high on the priority list for good guys? Many website owners/security officers are not necessarily aware of the underlying tech that powers their website. For example, if you install Wordpress, the most popular content management system on the Internet, you get PHP on your server.
Ironically, PHP applications are the most prevalent, in terms of absolute numbers, in the web, hence a strong interest by attackers. Most web applications are PHP based because this is the platform of choice for small, low cost applications, and most applications on the web are small, low cost, applications.
Today, some very popular sites are actively using PHP, including:
- Facebook.com
- Baidu.com
- Wikipedia.org
- Qq.com
- Taobao.com
- Sina.com.cn
- Wordpress.com
- Weibo.com
- 163.com
- Soso.com
Sites using PHP only recently:
- Soso.com
- Reuters.com
- Wsj.com
- Forbes.com
RFI/LFI primarily affects web applications written in the PHP programming language. PHP is a general-purpose server-side scripting language originally designed for Web development to produce dynamic Web pages. It is among one of the first developed server-side scripting languages to be embedded into an HTML source document, rather than calling an external file to process data. Ultimately, the code is interpreted by a Web server with a PHP processor module which generates the resulting Web page. PHP can be deployed on most Web servers and also as a standalone shell on almost every operating system and platform free of charge.[4]
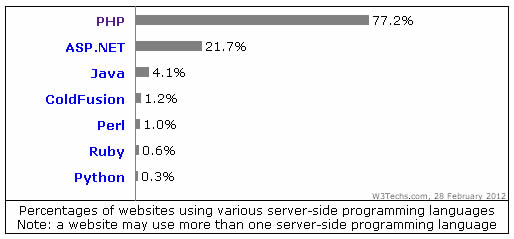
PHP is by far the most popular server-side programming language. As of February 28th of 2012, PHP is used by 77.2% of the internet top Alexa ranked million websites.[5] For comparison, the runner-up technology (MS ASP.NET) is used on only 21.7% of these sites. The use of PHP is also very frequent on the most visited sites, as four of top Alexa ranked ten web sites are powered by PHP (Facebook, Baidu.com, Wikipedia, QQ.COM). Looking at these numbers, it becomes very clear why PHP is a prime target for hackers—and equally perplexing why security teams are neglecting it.
Further examination of The PHP versions break down, shows that PHP subversion 5.2 is the most popular version in the wild and that about 90% of deployed PHP enabled server are of version 5.2 or above.
[1] http://www.imperva.com/docs/HII_Web_Application_Attack_Report_Ed2.pdf
[2] http://blog.imperva.com/2011/06/analyzing-the-lulzsec-attacks-.html
[3] http://markmaunder.com/2011/08/02/technical-details-and-scripts-of-the-wordpress-timthumb-php-hack/
[4] http://en.wikipedia.org/wiki/PHP
[5] http://w3techs.com/technologies/overview/programming_language/all